8i | 9i | 10g | 11g | 12c | 13c | 18c | 19c | 21c | 23c | Misc | PL/SQL | SQL | RAC | WebLogic | Linux
Home » Articles » Linux » Here
Linux Firewall (firewalld, firewall-cmd, firewall-config)
Fedora 18 introduced firewalld as a replacement for the previous iptables service. Since RHEL7 and Oracle Linux 7 are based on Fedora 19, the switch from iptables service to firewalld is now part of the Enterprise Linux distributions. This article is a rework of the previous Linux Firewall article, bringing it up to date.
You need to distinguish between the iptables service and the iptables command. Although firewalld is a replacement for the firewall management provided by iptables service, it still uses the iptables command for dynamic communication with the kernel packet filter (netfilter). So it is only the iptables service that is replaced, not the iptables command. That can be a confusing distinction at first.
- Reverting to the iptables Service
- Installation
- firewall-config
- firewall-cmd
- Backups and Transfers of Firewall Configuration
- Quick Database Setup
Related articles.
Reverting to the iptables Service
If you are not ready to make the break to firewalld, you can still use the iptables service by issuing the following commands.
# systemctl stop firewalld # systemctl disable firewalld # iptables-service # touch /etc/sysconfig/iptables # systemctl start iptables # systemctl enable iptables # touch /etc/sysconfig/ip6tables # systemctl start ip6tables # systemctl enable ip6table
From this point forward, firewall administration will be similar to that described here.
The rest of this article assumes you are going to use firewalld.
Installation
Most installations will include the firewall functionality, but if you need to manually install it, do the following.
# yum install firewalld firewall-config
Make sure the service is started and will auto-start on reboot.
# systemctl start firewalld.service # systemctl enable firewalld.service
You can check the current status of the service using the following command.
# systemctl status firewalld
firewalld.service - firewalld - dynamic firewall daemon
Loaded: loaded (/usr/lib/systemd/system/firewalld.service; enabled)
Active: active (running) since Sun 2014-04-20 14:06:46 BST; 30s ago
Main PID: 13246 (firewalld)
CGroup: /system.slice/firewalld.service
└─13246 /usr/bin/python /usr/sbin/firewalld --nofork --nopid
Apr 20 14:06:44 localhost.localdomain systemd[1]: Starting firewalld - dynamic firewall daemon...
Apr 20 14:06:46 localhost.localdomain systemd[1]: Started firewalld - dynamic firewall daemon.
#
To disable the firewall, run the following commands.
# systemctl stop firewalld.service # systemctl disable firewalld.service
firewall-config
The GUI screen to control the firewall is available from the menu.
- Fedora : System > Administration > Firewall
- RHEL7/OL7 : Applications > Sundry > Firewall
Alternatively, if can be started from the command line using the firewall-config command. If it is not already present, it can be installed using the following command.
# yum install firewall-config
Once started, the "Configuration:" drop-down allows you to decide if you are modifying currently running settings (Runtime) or those saved for future use (Permanent). You can also configure basic trusted services, such as SSH, FTP and HTTP, by putting a tick in the appropriate checkbox. All changes are applied immediately.
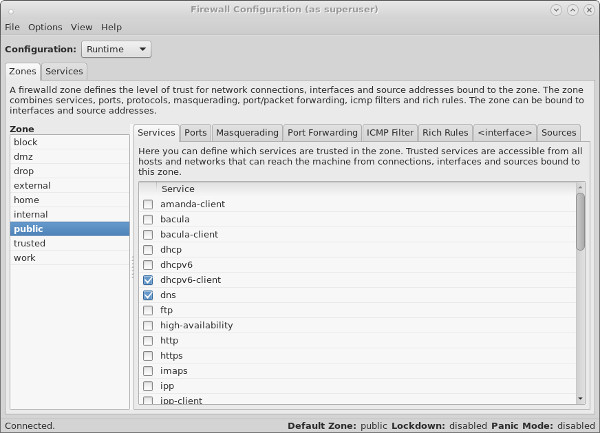
The "Ports" tab allows you to manually open ports that are not covered in the "Trusted Services" section.
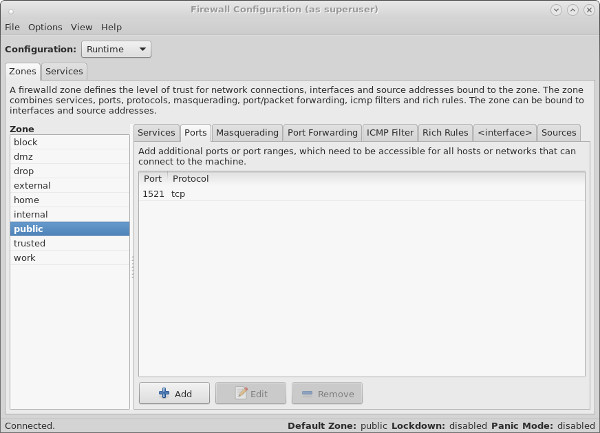
Remember, changes to the runtime configuration will be lost after the next reboot. If in doubt, make all changes to the permanent configuration and reload the runtime configuration using the "Options > Reload Firewalld" menu option.
firewall-cmd
In addition to the GUI interface, the firewall rules can be amended directly using the firewall-cmd command. The full extent of the firewall configuration is beyond the scope of this article, so instead a few specific examples will be given to allow you to get a feel for it. This article also assumes you have a single network interface and are happy to keep it set to the default zone (public).
The firewall-cmd usage notes are displayed when you use the "-h" or "--help" options.
# firewall-cmd --help
Check the current top-level firewall configuration using the following commands.
# Check firewall state. firewall-cmd --state # Check active zones. firewall-cmd --get-active-zones # Check current active services. firewall-cmd --get-service # Check services that will be active after next reload. firewall-cmd --get-service --permanent
Lock down and unlock the firewall using the following commands.
# firewall-cmd --panic-on success # firewall-cmd --query-panic yes # firewall-cmd --panic-off success # firewall-cmd --query-panic no #
Reload the runtime configuration from the permanent files using the following command.
# firewall-cmd --reload
The firewall comes with predefined services, which are XML files is the "/usr/lib/firewalld/services/" directory.
# ls /usr/lib/firewalld/services/ amanda-client.xml http.xml libvirt.xml pmwebapis.xml ssh.xml bacula-client.xml imaps.xml mdns.xml pmwebapi.xml telnet.xml bacula.xml ipp-client.xml mountd.xml pop3s.xml tftp-client.xml dhcpv6-client.xml ipp.xml ms-wbt.xml postgresql.xml tftp.xml dhcpv6.xml ipsec.xml mysql.xml proxy-dhcp.xml transmission-client.xml dhcp.xml kerberos.xml nfs.xml radius.xml vnc-server.xml dns.xml kpasswd.xml ntp.xml rpc-bind.xml wbem-https.xml ftp.xml ldaps.xml openvpn.xml samba-client.xml high-availability.xml ldap.xml pmcd.xml samba.xml https.xml libvirt-tls.xml pmproxy.xml smtp.xml #
You shouldn't edit these. Instead, copy a specific service file to the "/etc/firewalld/services/" directory and editing it there. The firewalld service always uses files in "/etc/firewalld/services/" directory in preference to those in the "/usr/lib/firewalld/services/" directory. Remember to reload the config after making any changes.
# firewall-cmd --reload
As with the GUI interface, you need to decide if you want to make changes to either the runtime configuration, permanent configuration or both. If you want to set both the runtime and permanent configuration you have two choices. Set them both independently, or set the permanent configuration and reload the firewall.
Add an existing service to a zone.
# # Set runtime and permanent independently. # firewall-cmd --zone=public --add-service=https # firewall-cmd --permanent --zone=public --add-service=https or # # Set permanent and reload the runtime config. # firewall-cmd --permanent --zone=public --add-service=https # firewall-cmd --reload
All subsequent examples will assume you want to amend both the runtime and permanent configuration and will only set the permanent configuration and then reload the runtime configuration.
Once you've amended the default configuration, the "/etc/firewalld/zones/public.xml" file will be created. You can manually amend this file, but you will need to issue a reload for the changes to take effect.
Check the services in a zone.
# firewall-cmd --zone=public --list-services dhcpv6-client https ss # firewall-cmd --permanent --zone=public --list-services dhcpv6-client https ss #
Remove a service from a zone.
# firewall-cmd --permanent --zone=public --remove-service=https # firewall-cmd --reload
Open a specific port or range in a zone, check its runtime and permanent configuration, then remove it.
# firewall-cmd --permanent --zone=public --add-port=8080-8081/tcp # firewall-cmd --reload # firewall-cmd --zone=public --list-ports 8080-8081/tcp # firewall-cmd --permanent --zone=public --list-ports 8080-8081/tcp # # firewall-cmd --permanent --zone=public --remove-port=8080-8081/tcp # firewall-cmd --reload
Rich rules allow you to create more complex configurations. The following command allows you to open HTTP access to a specific IP address.
# firewall-cmd --permanent --zone=public --add-rich-rule="rule family="ipv4" \
source address="192.168.0.4/24" service name="http" accept"
The "/etc/firewalld/zones/public.xml" file now contains the rich rule.
<?xml version="1.0" encoding="utf-8"?>
<zone>
<short>Public</short>
<description>For use in public areas. You do not trust the other computers on networks
to not harm your computer. Only selected incoming connections are accepted.</description>
<service name="dhcpv6-client"/>
<service name="ssh"/>
<rule family="ipv4">
<source address="192.168.0.4/24"/>
<service name="http"/>
<accept/>
</rule>
</zone>
The rule can be removed directly from the XML file, or removed using the "--remove-rich-rule" option.
# firewall-cmd --permanent --zone=public --remove-rich-rule="rule family="ipv4" \
source address="192.168.0.4/24" service name="http" accept"
The following example opens and closes port 8080 for a specific source IP address using a rich rule.
# firewall-cmd --permanent --zone=public --add-rich-rule="rule family="ipv4" \
source address="192.168.0.4/24" \
port protocol="tcp" port="8080" accept"
# cat /etc/firewalld/zones/public.xml
<?xml version="1.0" encoding="utf-8"?>
<zone>
<short>Public</short>
<description>For use in public areas. You do not trust the other computers on networks
to not harm your computer. Only selected incoming connections are accepted.</description>
<service name="dhcpv6-client"/>
<service name="ssh"/>
<rule family="ipv4">
<source address="192.168.0.4/24"/>
<port protocol="tcp" port="8080"/>
<accept/>
</rule>
</zone>
#
# firewall-cmd --permanent --zone=public --remove-rich-rule="rule family="ipv4" \
source address="192.168.0.4/24" \
port protocol="tcp" port="8080" accept"
Backups and Transfers of Firewall Configuration
As all non-default configuration is placed under the "/etc/firewalld/" directory, taking a copy of the contents of this directory and its sub-directories constitutes a backup of the firewall configuration.
Not surprisingly, transferring the contents of this directory will allow you to duplicate the firewall configuration in other servers.
Quick Database Setup
If you are using the server as an Oracle database server, you will probably want to make sure the SSH and Oracle listener ports are accessible. You could lock these down to specific source IP addresses, but for a quick setup, you could just do the following, where "1521" is the port used for the listener.
# systemctl start firewalld.service # systemctl enable firewalld.service # firewall-cmd --permanent --zone=public --add-port=22/tcp # firewall-cmd --permanent --zone=public --add-port=1521/tcp # firewall-cmd --reload # firewall-cmd --permanent --zone=public --list-ports 1521/tcp 22/tcp #
For more information see:
- Security Guide : Using Firewalls (RHEL7)
- RHEL Documentation
- FirewallD
- Linux man pages
- Linux Firewall (iptables, system-config-firewall)
Hope this helps. Regards Tim...