8i | 9i | 10g | 11g | 12c | 13c | 18c | 19c | 21c | 23c | Misc | PL/SQL | SQL | RAC | WebLogic | Linux
Home » Articles » Linux » Here
Linux Unified Key Setup (LUKS) Encrypted File Systems
This article explains how to create and mount Linux Unified Key Setup (LUKS) encrypted file systems, with specific reference to the information needed for the RHCSA EX200 and RHCE EX300 certification exams.
Remember, the exams are hands-on, so it doesn't matter which method you use to achieve the result, so long as the end product is correct.
- During Installation (Disk Druid)
- Disk Utility
- Manual Setup (cryptsetup)
- Persistent Mounts (crypttab, fstab)
Related articles.
- Linux Disk Partitioning (fdisk, parted)
- Linux File Systems (mkfs, mount, fstab)
- Linux Logical Volume Management
During Installation (Disk Druid)
In many cases, encryption of volumes will take place during the installation process. When prompted for the installation type, check the "Encrypt system" option to encrypt all partitions except the boot partition.
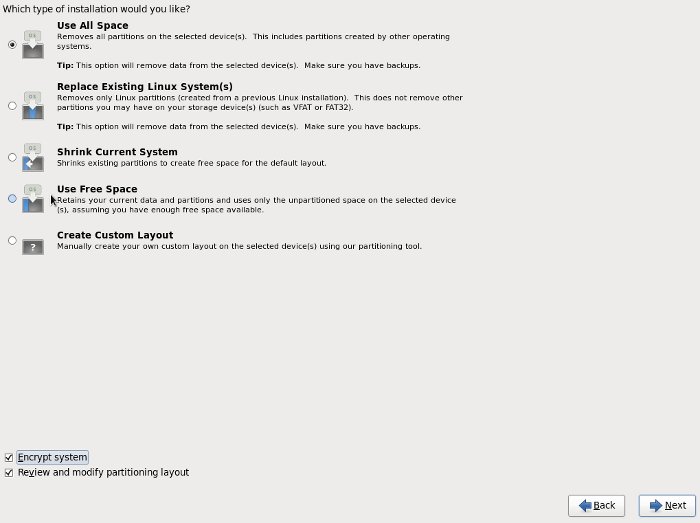
You can also choose to encrypt individual partitions by unchecking the "Encrypt system" option and checking the "Review and modify partitioning layout" option on the previous screen. Highlighting a specific volume and clicking the "Edit" button allows you to check the "Encrypt" checkbox for that individual volume.
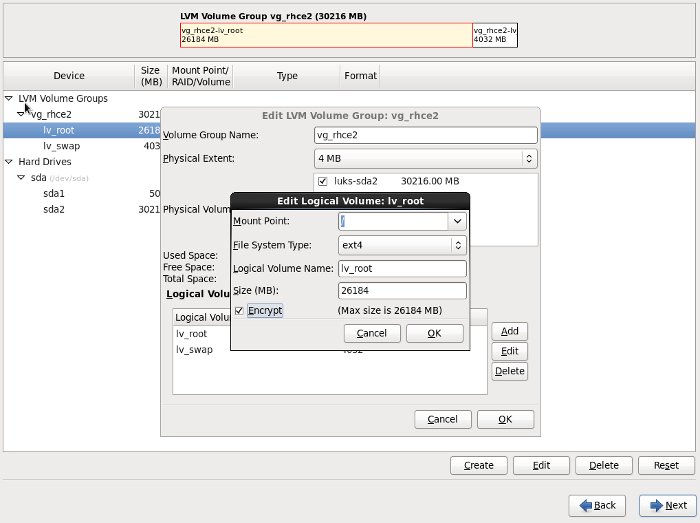
You will be prompted for an encryption password when you click the "Next" button to leave the main screen.
Disk Utility
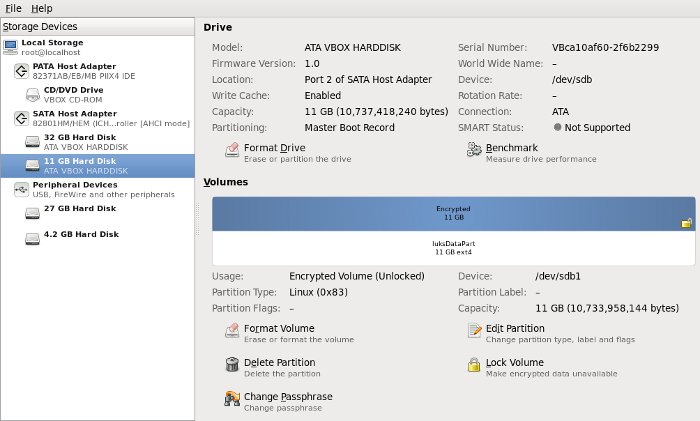
The Disk Utility (Applications > System Tools > Disk Utility) can create encrypted volumes directly. Once it is started, highlight the drive of interest and click the "+ Create Partition" button.
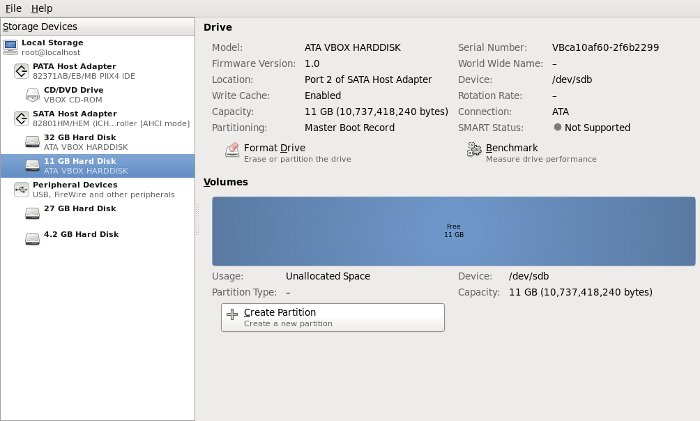
Enter the required partition details, including a suitable name. The name is used in the device-mapper mappings. Check the "Encrypt underlying device" checkbox and click the "Create" button.
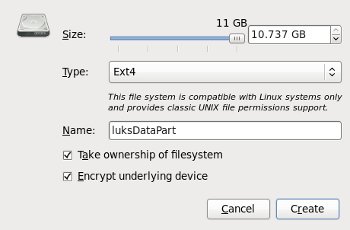
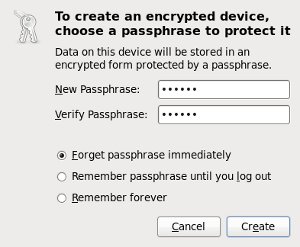
Enter an encryption password and click the "Create" button.
The details of the encrypted partition are now displayed in the main screen.
Manual Setup (cryptsetup)
Check the cryptsetup-luks package is installed on the system.
# rpm -q cryptsetup-luks cryptsetup-luks-1.2.0-6.el6.x86_64 #
If not, install it from a yum repository.
# yum install cryptsetup-luks
Create a new partition. In this case it spans the whole 10G virtual drive.
# fdisk /dev/sdb
WARNING: DOS-compatible mode is deprecated. It's strongly recommended to
switch off the mode (command 'c') and change display units to
sectors (command 'u').
Command (m for help): c
DOS Compatibility flag is not set
Command (m for help): u
Changing display/entry units to sectors
Command (m for help): n
Command action
e extended
p primary partition (1-4)
p
Partition number (1-4): 1
First sector (2048-20971519, default 2048):
Using default value 2048
Last sector, +sectors or +size{K,M,G} (2048-20971519, default 20971519):
Using default value 20971519
Command (m for help): w
The partition table has been altered!
Calling ioctl() to re-read partition table.
Syncing disks.
[root@rhce1 dev]#
For extra security you may wish to fill the volume with random data before continuing. You can use either of the following commands to achieve this.
# badblocks -c 10240 -s -w -t random -v /dev/sdb1 # dd if=/dev/urandom of=/dev/sdb1
The cryptsetup command is used to setup the dm-crypt device-mapper mappings.
# cryptsetup --verbose --verify-passphrase luksFormat /dev/sdb1 WARNING! ======== This will overwrite data on /dev/sdb1 irrevocably. Are you sure? (Type uppercase yes): YES Enter LUKS passphrase: Verify passphrase: Command successful. #
The LUKS encrypted volume is then opened using the password specified earlier.
# cryptsetup luksOpen /dev/sdb1 luksDataPart Enter passphrase for /dev/sdb1: #
The last parameter will be used in the device-mapper mapping, so in this case the mapping will be "/dev/mapper/luksDataPart".
# ls -l /dev/mapper | grep luksDataPart lrwxrwxrwx. 1 root root 7 Feb 21 12:11 luksDataPart -> ../dm-2 #
A file system can now be created on the volume in the normal way.
# mkfs.ext4 /dev/mapper/luksDataPart mke2fs 1.41.12 (17-May-2010) Filesystem label= OS type: Linux Block size=4096 (log=2) Fragment size=4096 (log=2) Stride=0 blocks, Stripe width=0 blocks 655360 inodes, 2620672 blocks 131033 blocks (5.00%) reserved for the super user First data block=0 Maximum filesystem blocks=2684354560 80 block groups 32768 blocks per group, 32768 fragments per group 8192 inodes per group Superblock backups stored on blocks: 32768, 98304, 163840, 229376, 294912, 819200, 884736, 1605632 Writing inode tables: done Creating journal (32768 blocks): done Writing superblocks and filesystem accounting information: done This filesystem will be automatically checked every 36 mounts or 180 days, whichever comes first. Use tune2fs -c or -i to override. #
The resulting file system is mounted just like any other file system. For example, the following script creates a mount point, then mounts and unmounts the encrypted volume.
# mkdir /sensitive_data # mount /dev/mapper/luksDataPart /sensitive_data # # umount /sensitive_data
If you wish, you can close the encrypted volume using the following command.
# cryptsetup luksClose /dev/mapper/luksDataPart
Persistent Mounts (crypttab, fstab)
To automatically mount an encrypted volume on reboot, add the following entry to the "/etc/crypttab" file. The first parameter is the device-mapper name. The second is the device path for the partition. Setting the last parameter to "none" means the system will prompt for the encryption password on reboot.
luksDataPart /dev/sdb1 none
Add the mount information to the "/etc/fstab" file.
/dev/mapper/luksDataPart /sensitive_data ext4 defaults 1 2
If you are using SELinux, you will need to restore the default SELinux contexts.
# /sbin/restorecon -v -R /sensitive_data /sbin/restorecon reset /sensitive_data context system_u:object_r:file_t:s0->system_u:object_r:default_t:s0 /sbin/restorecon reset /sensitive_data/lost+found context system_u:object_r:file_t:s0->system_u:object_r:default_t:s0 #
On reboot, the console should prompt for the password for any encrypted volumes. When you see the following prompt, enter the password followed by return.
/sensitive_data is password protected:
If you get any of the setup wrong, the reboot will fail and you will be left at the file system repair prompt. Enter the root password and remount the root file system.
# mount -w -o remount /
You can now attempt to fix the issue, or simply remove the entry from the "/etc/fstab" file and reboot.
If you want volumes to mount automatically, with no password prompt, you must provide the password in a file.
# dd if=/dev/random of=/root/luks.key bs=32 count=1 0+1 records in 0+1 records out 23 bytes (23 B) copied, 0.000196781 s, 117 kB/s # cryptsetup luksAddKey /dev/sdb1 /root/luks.key Enter any passphrase: #
The third parameter of the "/etc/crypttab" should be changed from "none" to the path of the password file.
luksDataPart /dev/sdb1 /root/luks.key
If you allow password-less reboots, the information will only be protected if the drives are stolen, not if the whole system is stolen.
For more information see:
Hope this helps. Regards Tim...