8i | 9i | 10g | 11g | 12c | 13c | 18c | 19c | 21c | 23ai | Misc | PL/SQL | SQL | RAC | WebLogic | Linux
Oracle Cloud Infrastructure (OCI) : Create a Bastion
This article shows how to create a bastion under Oracle Cloud Infrastructure (OCI).
The screens change a little with each quarterly release of Oracle Cloud. Even so, the screen shots in this article will give you a good idea of what is involved.
Related articles.
- Oracle Cloud Infrastructure (OCI) : Create a Compartment
- Oracle Cloud Infrastructure (OCI) : Create a Virtual Cloud Network (VCN)
- Oracle Cloud Infrastructure (OCI) : Create a Compute VM
- Cloud Articles
What is a Bastion?
Allowing direct connections to cloud services and resources can present a security risk, especially as the number of resources grow over time. To solve this, some people use a small virtual machine inside the virtual cloud network and make connections to all the cloud services from that VM. This reduces the number of services exposed to the outside world, whilst still allowing connections for developers and administrators. We can consider a small VM like this to be a manual version of a bastion, or a jump-box.
An alternative to creating a manual bastion is to use an Oracle Cloud Infrastructure (OCI) Bastion. This article shows how to create a bastion under Oracle Cloud Infrastructure (OCI).
Before we move on, here are some assumptions.
- This article assumes you've already defined a Compartment, Virtual Cloud Network (VCN) and Compute instance (VM). You can see how to do that in the linked articles.
- In this example we create a session to a VM, but this could be any supported "host:port" combination.
Create a Bastion
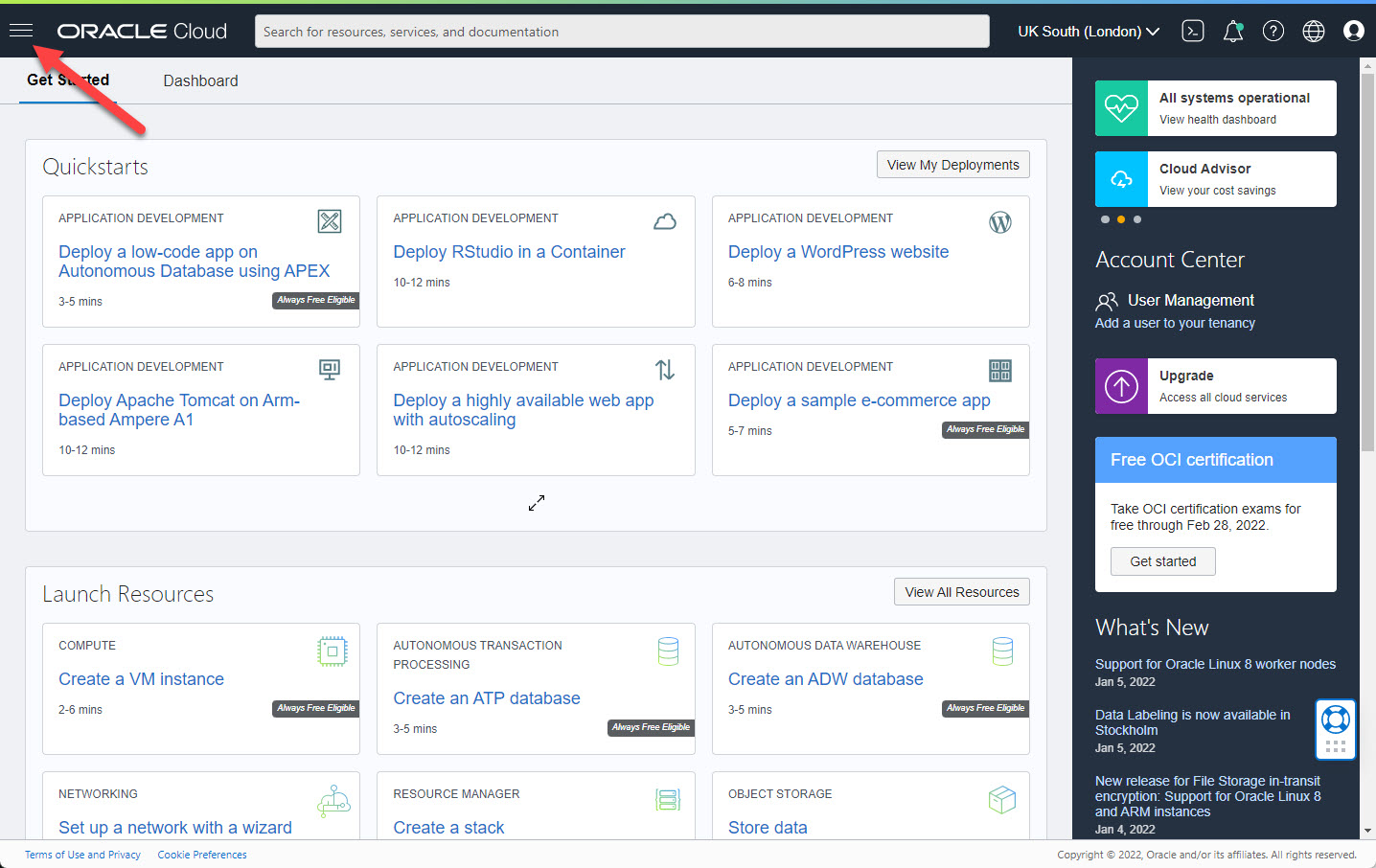
Log into the Oracle Cloud. Click on the hamburger menu at the top-left of the screen.
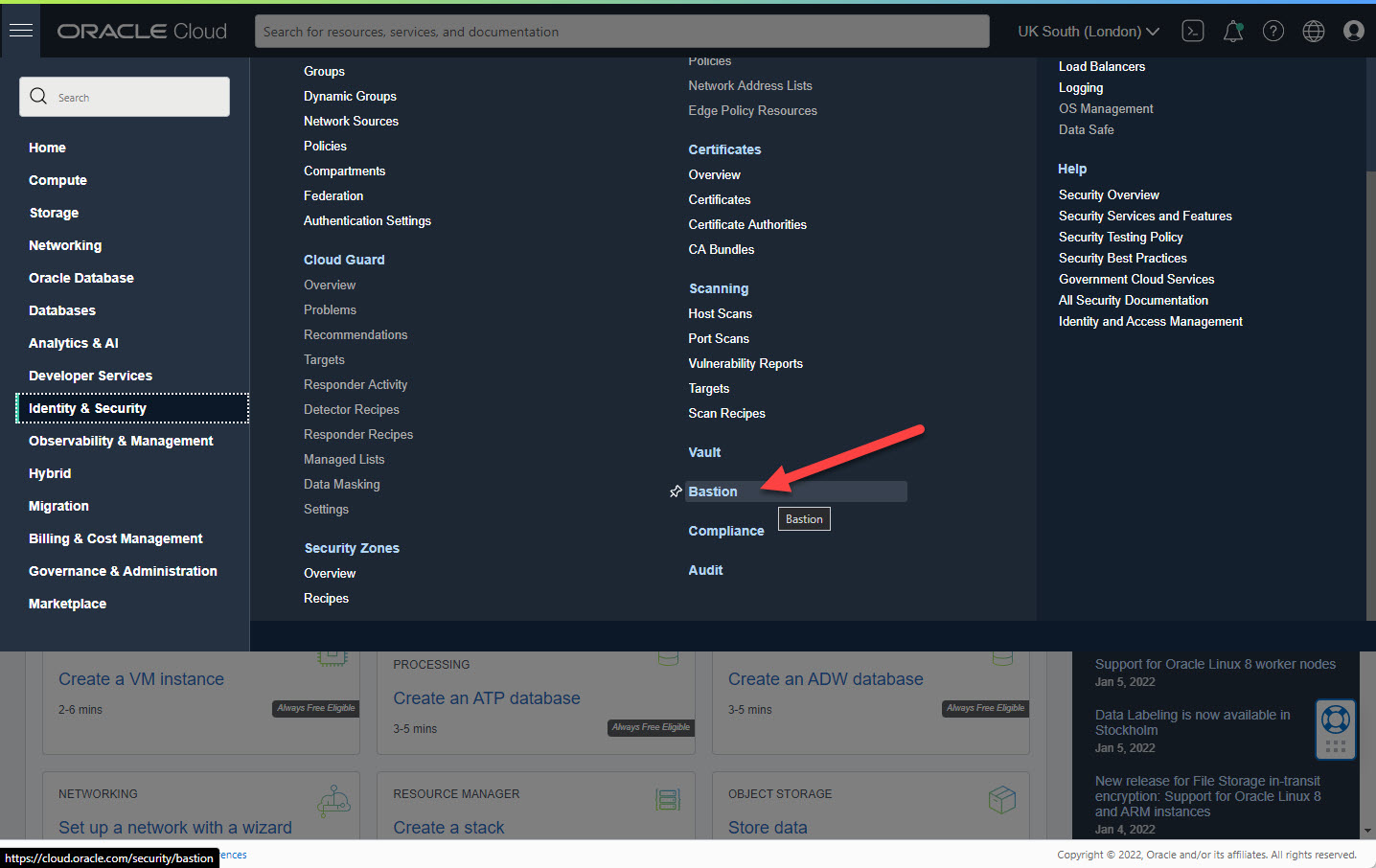
On the menu select "Identity & Security > Bastion".
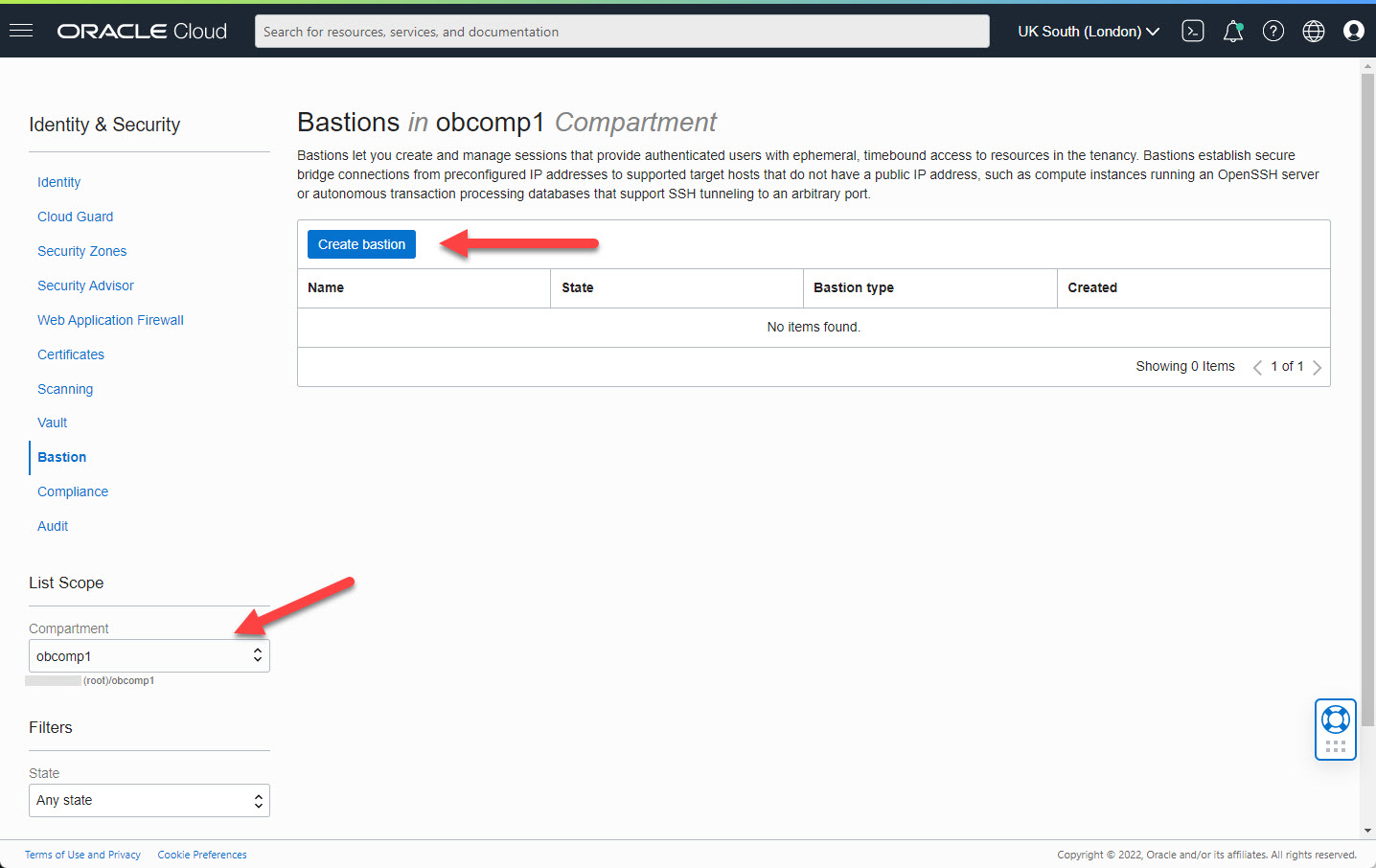
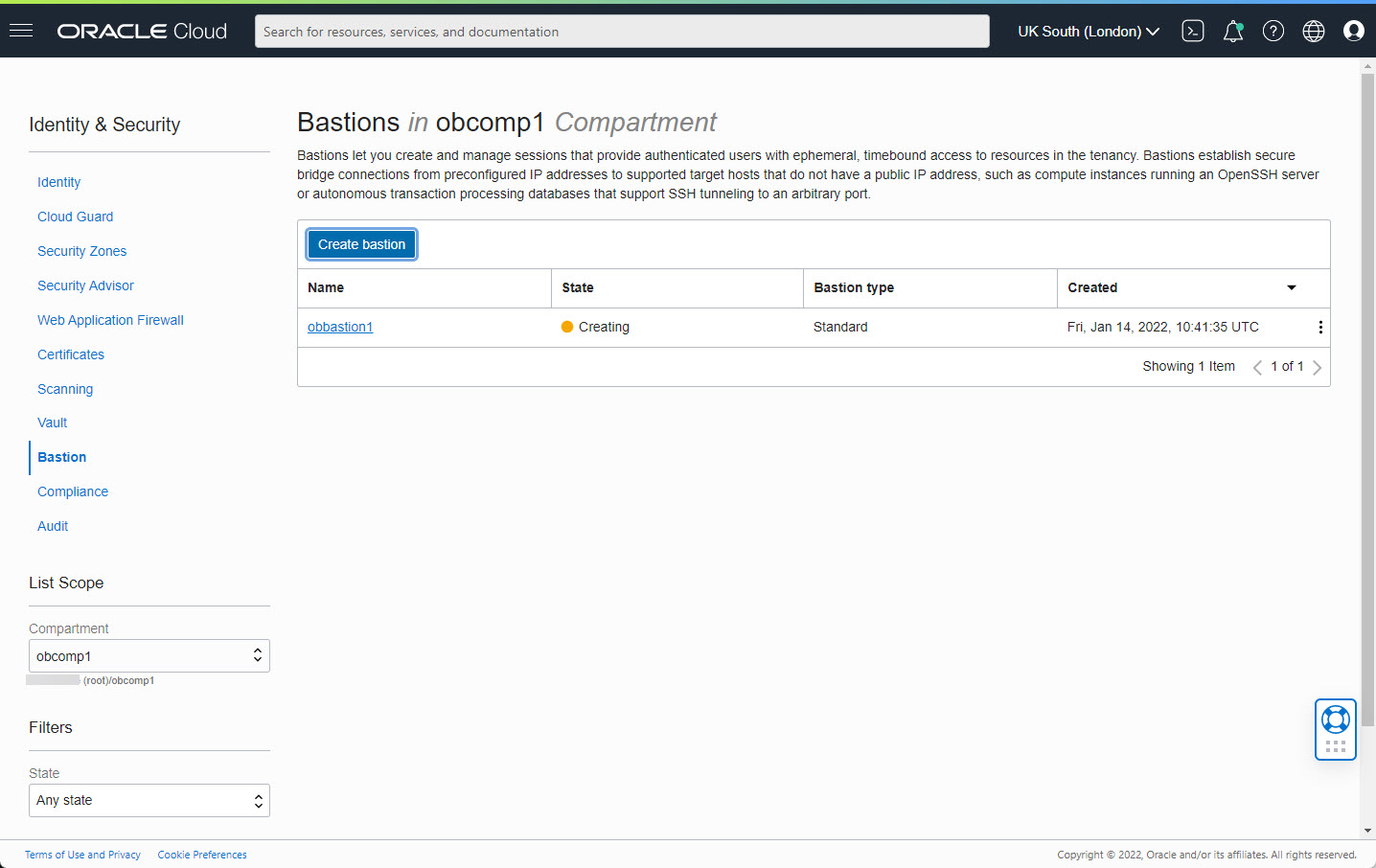
Select the compartment and click the "Create bastion" button.
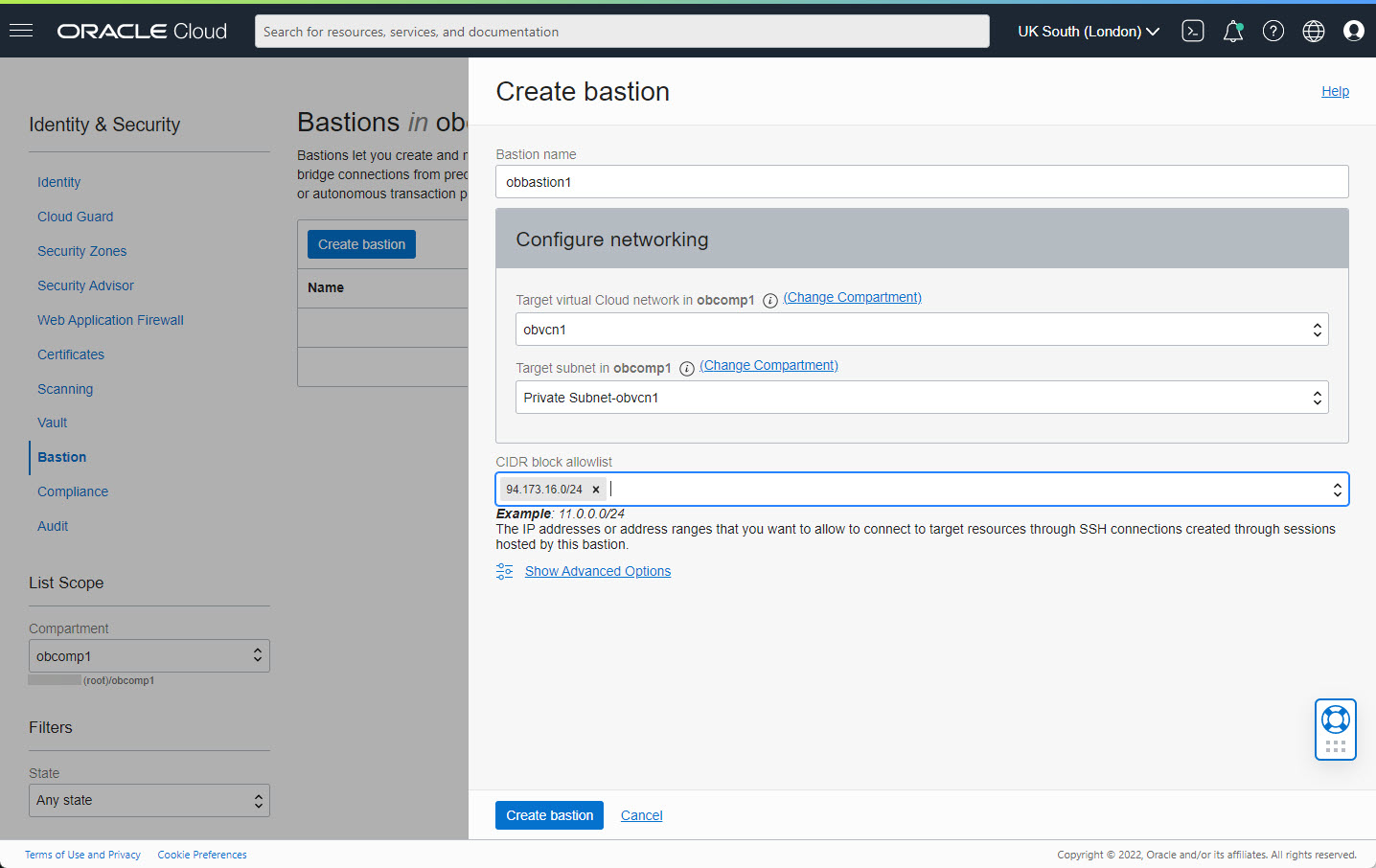
Enter the bastion name and select the VCN and subnet for the bastion. We need to enter a CIDR block allowlist. In this case I've used the subnet for my IP address from my internet service provider. Click the "Create bastion" button.
Wait while the bastion is provisioned.
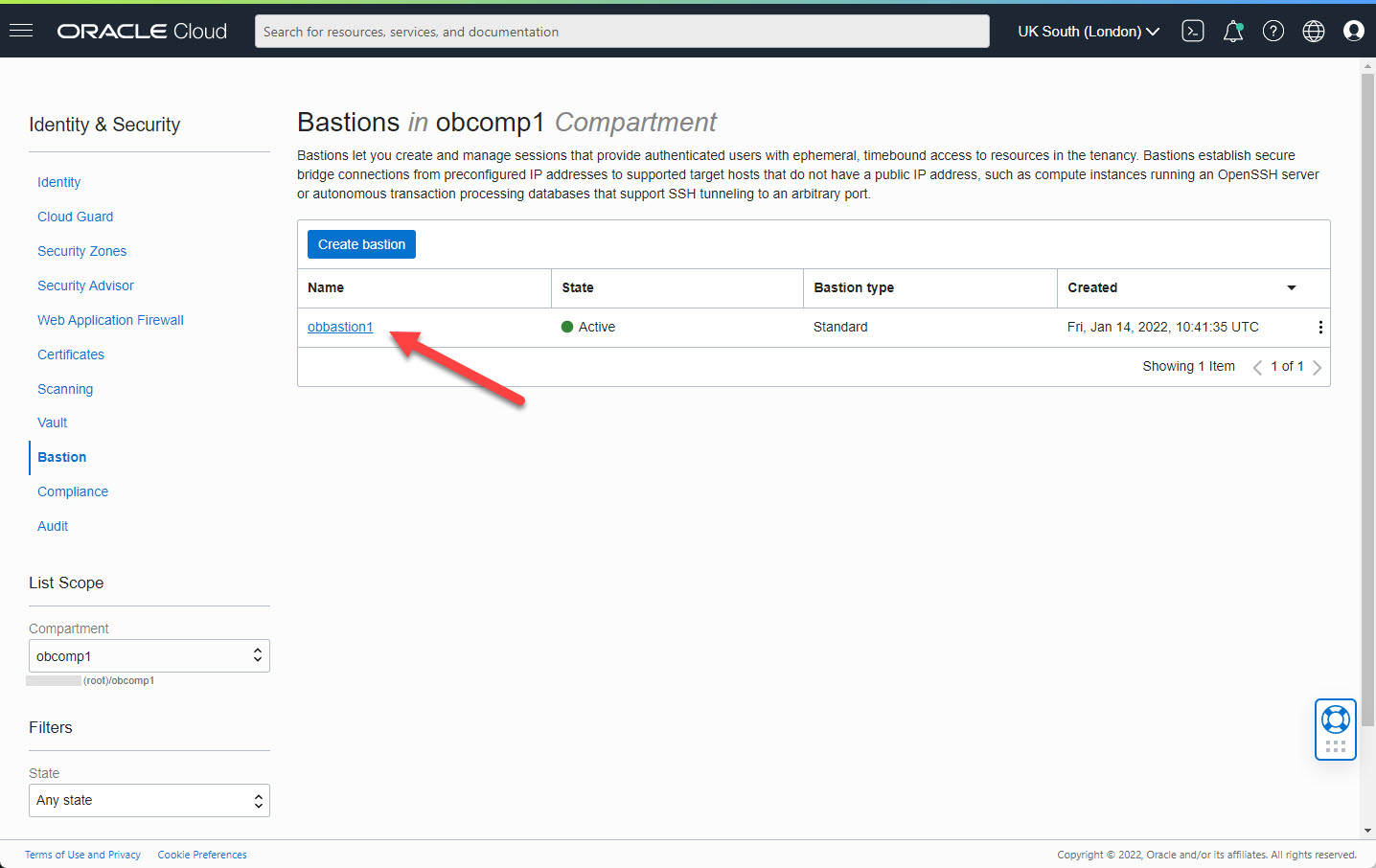
Once the bastion is created, click on the link.
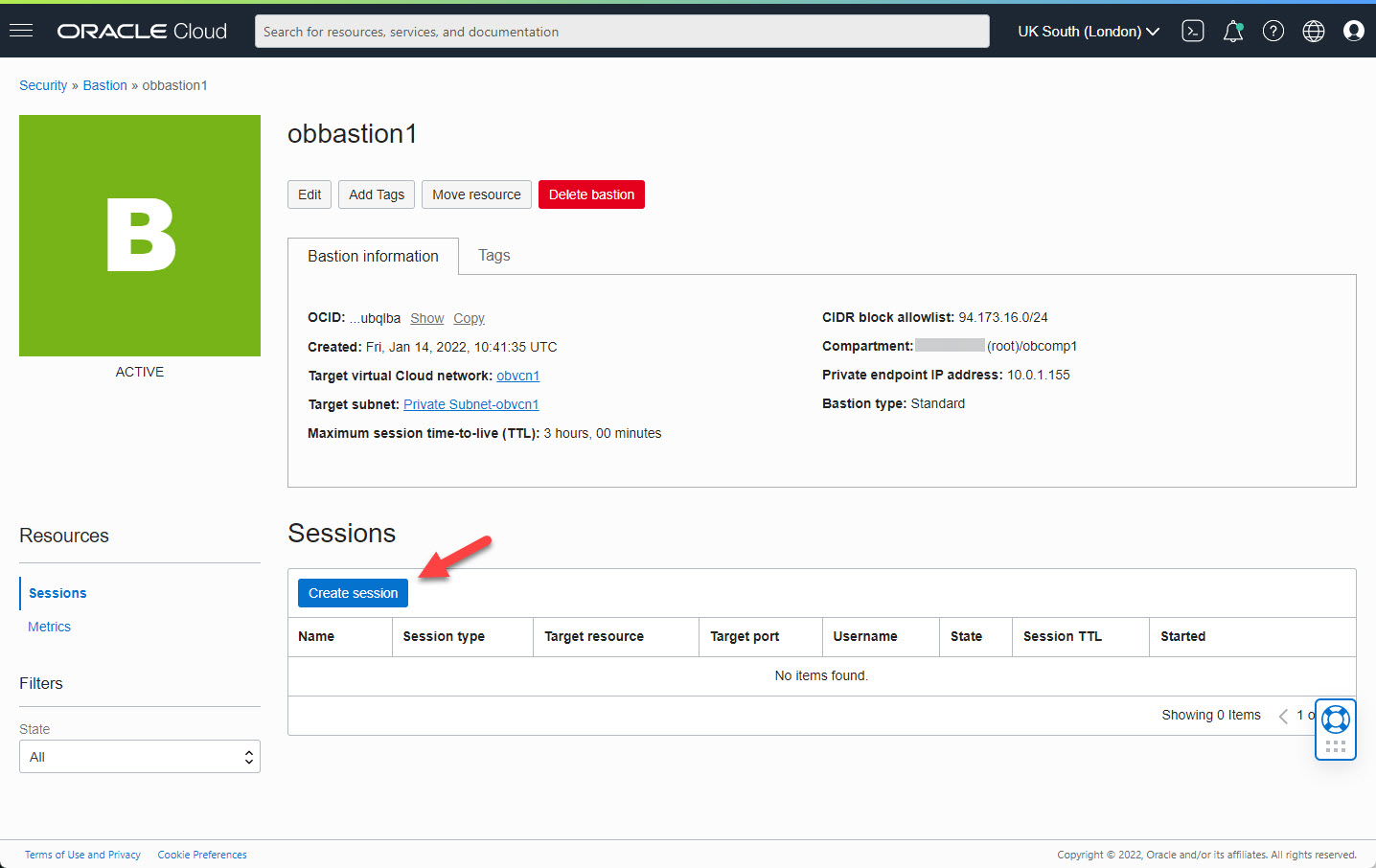
Click on the "Create session" button.
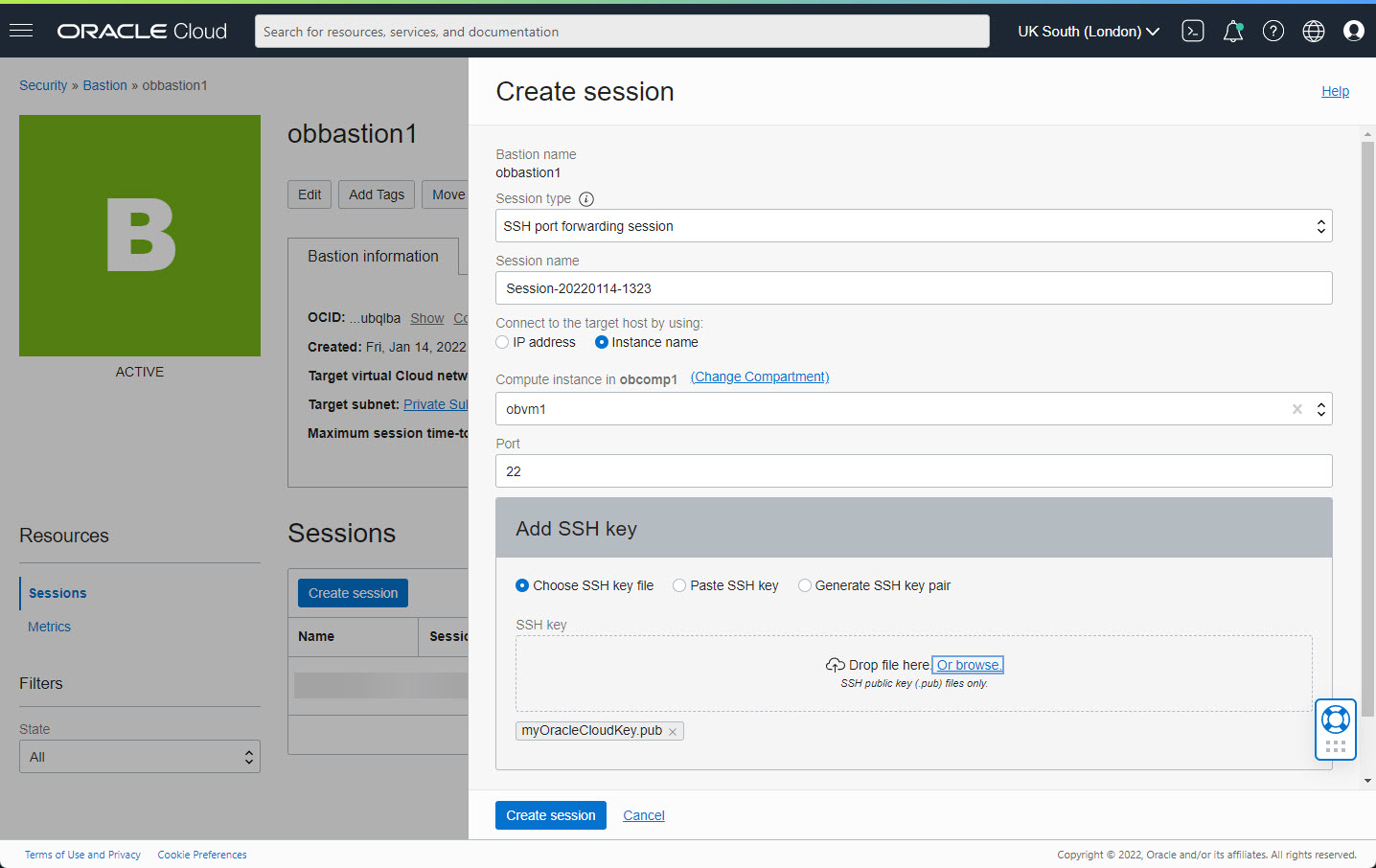
Select the type of session. In this case we used "SSH port forwarding session". Give the session a name, or accept the default name. Select the destination IP/Instance and port. Upload a private key to be used for the connection. Click the "Create session" button.
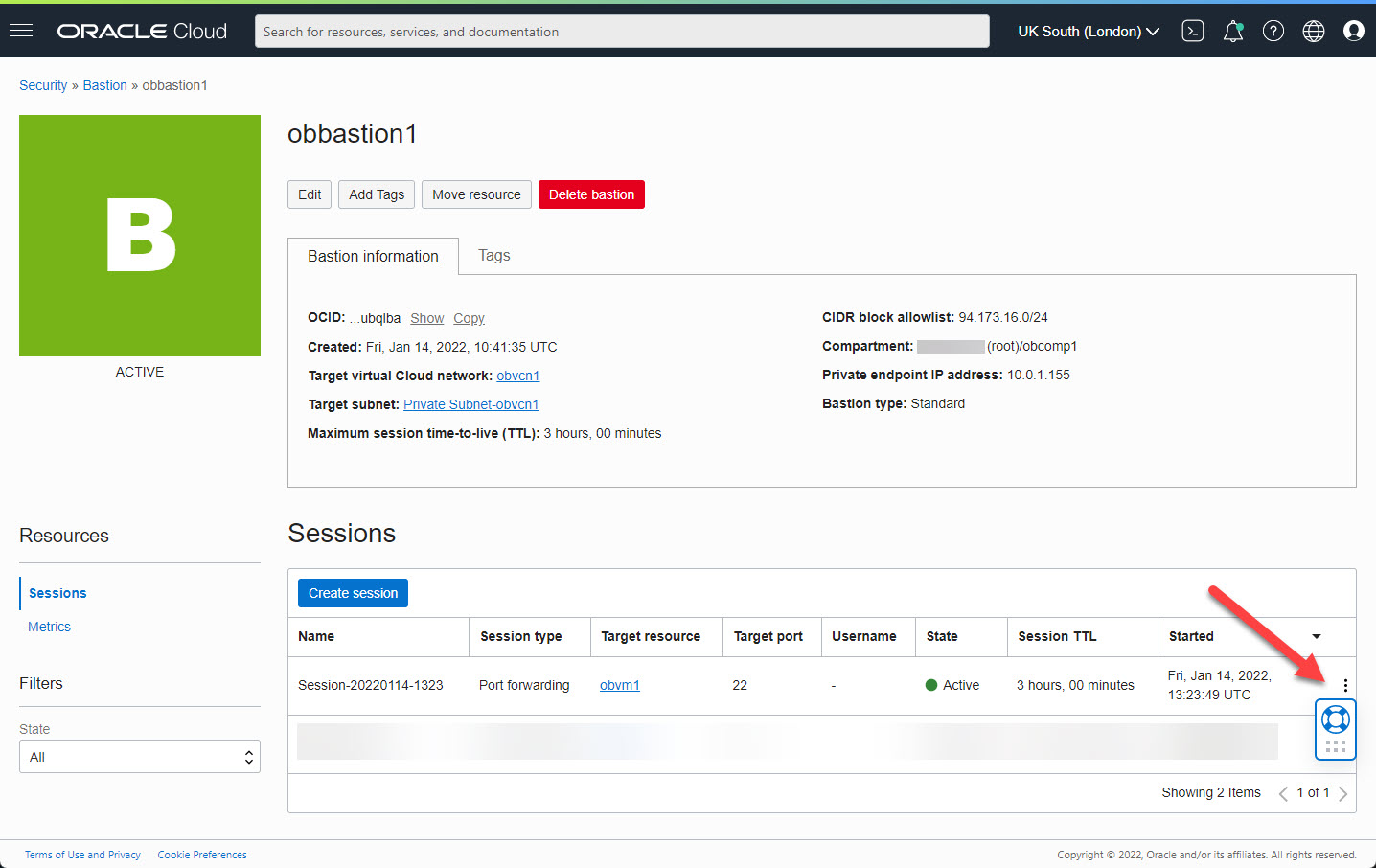
Click on the kebab menu on the right of the new session.
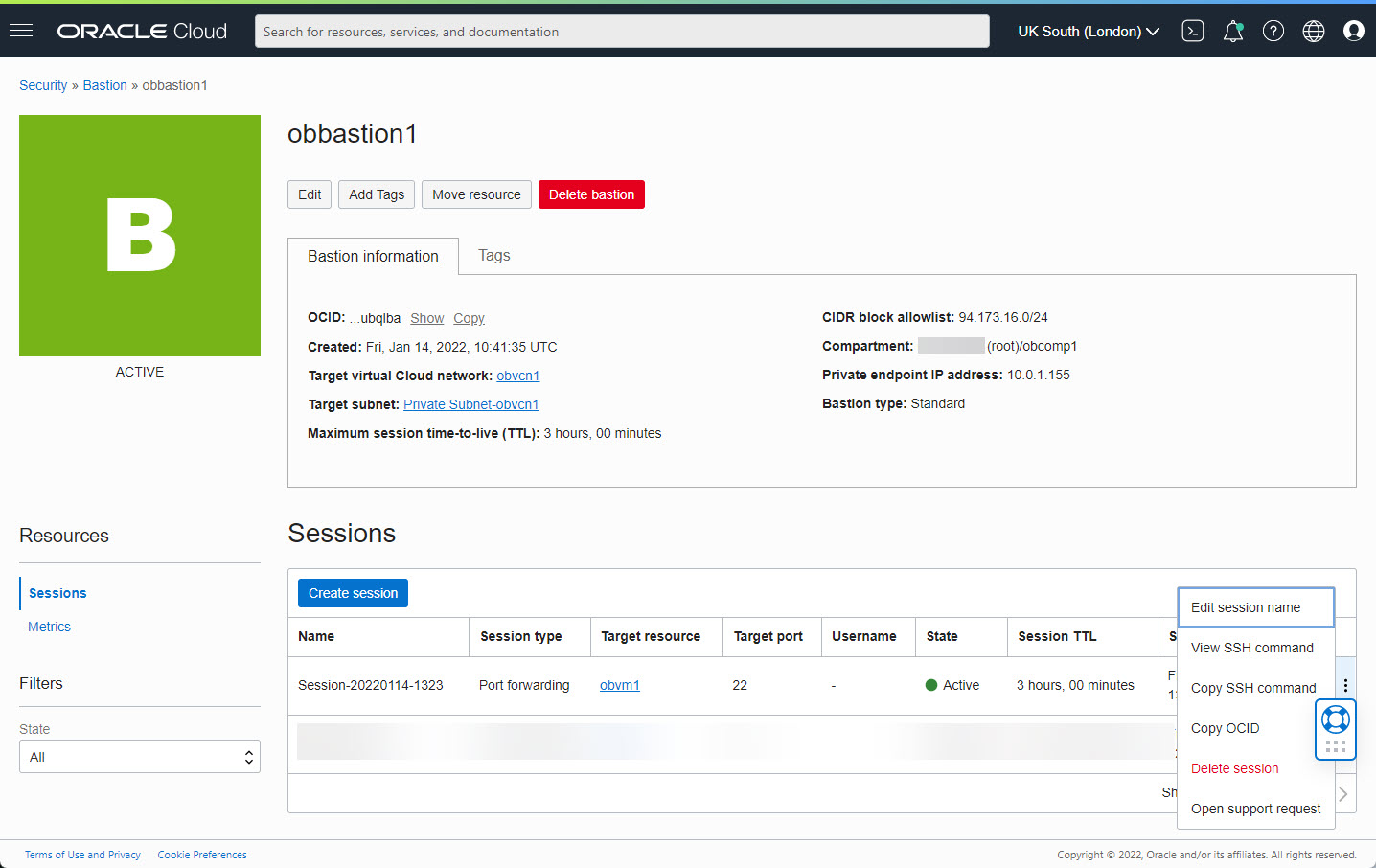
Click on the "Copy SSH command" option and paste the resulting text into an editor. We'll use it later.
Connect Using A Bastion
The connection details we copied previously will look something like this.
ssh -i-N -L :10.0.1.156:22 -p 22 ocid1.bastionsession.oc1.uk-london-1.amaa...3acq@host.bastion.uk-london-1.oci.oraclecloud.com
We use our private key and in this example I chose port 9022 for the local port to create the tunnel.
ssh -i ./myOracleCloudKey -N -L 9022:10.0.1.156:22 -p 22 ocid1.bastionsession.oc1.uk-london-1.amaa...3acq@host.bastion.uk-london-1.oci.oraclecloud.com
We can now make a connection to the destination server through the bastion using our tunnel.
ssh -i ./myOracleCloudKey opc@localhost -p 9022
Thoughts
Here are some thoughts about the current implementation of the Oracle Cloud Infrastructure (OCI) Bastion.
- The tunnel functionality seems to work fine.
- The "Managed SSH session" option requires the Bastion plugin to be enabled on the compute node. The plugins are listed on the "Oracle Cloud Agent" tab of the compute instance. Despite enabling this on my compute node, I was not able make Managed SSH sessions.
- The bastion will only work with an autonomous database if it has a private endpoint. Unfortunately configuring a private endpoint is not possible on free tier accounts. Without the private endpoint, we don't have access to the private IP address, so there is now way to reference our autonomous database from the bastion.
- For such a simple service, the current implementation feels quite clumsy. If feels like the minimum amount of work possible has been done to release this service. What I would like to see is when you pick an end point, the services does all configuration changes to allow you to connect to that end point, even if that means changing the networking on the destination services. At the moment it is up to you to make sure all the parts talk to each other, so it is no easier that creating your own manual bastion/jump box.
- Considering the current limitations, you may prefer to stick with your manual bastion at the moment.
For more information see:
- Bastion
- Oracle Cloud Infrastructure (OCI) : Create a Compartment
- Oracle Cloud Infrastructure (OCI) : Create a Virtual Cloud Network (VCN)
- Oracle Cloud Infrastructure (OCI) : Create a Compute VM
- Cloud Articles
Hope this helps. Regards Tim...