8i | 9i | 10g | 11g | 12c | 13c | 18c | 19c | 21c | 23c | Misc | PL/SQL | SQL | RAC | WebLogic | Linux
Oracle Cloud : MySQL Cloud Service - Create Service
The Oracle MySQL Cloud Service allows you to quickly deploy MySQL databases on the Oracle Public Cloud.
- Create SSH Key
- Create Service
- Connecting to the VM using SSH
- Firewall Rules
- Connecting to MySQL From a Remote Client
Create SSH Key
Before you start, you are going to need a key pair for authentication to your service.
$ ssh-keygen -b 2048 -t rsa -f myOracleCloudKey $ chmod 600 myOracleCloudKey*
Enter and confirm the passphrase when prompted. You will be asked to upload the public key during the service creation.
If you have any problems, or need instructions for using PuTTYgen on Windows, check out the documentation here.
Create Service
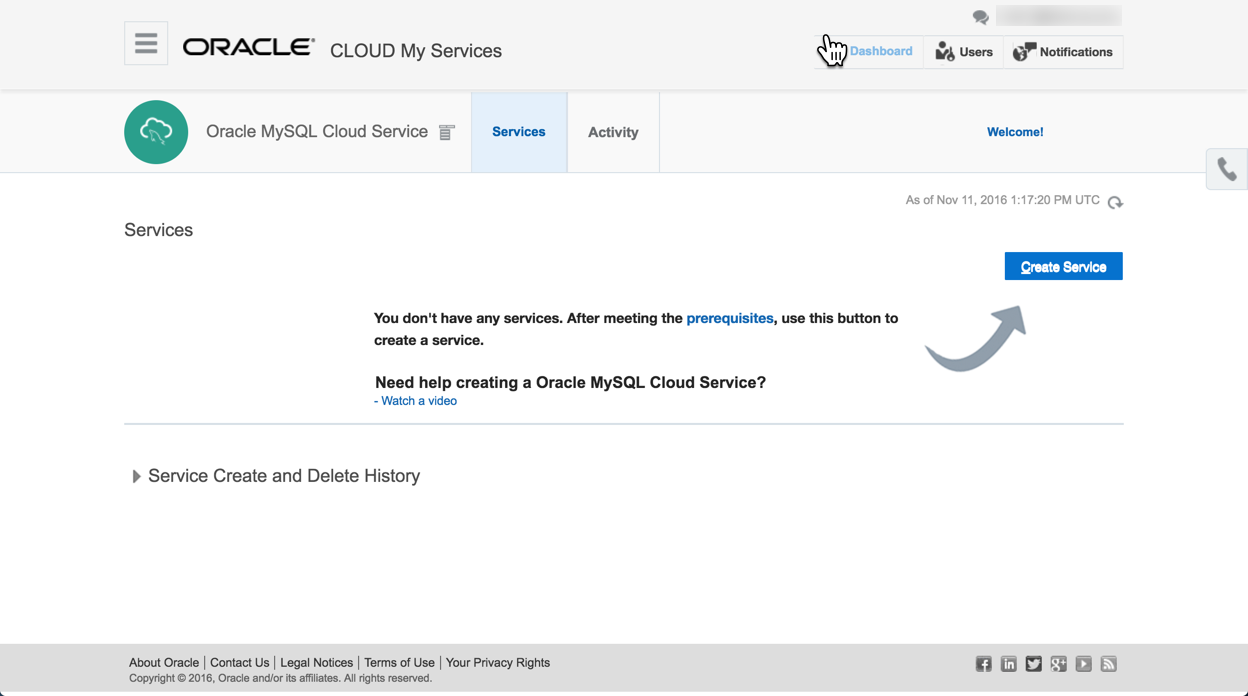
Navigate to the Oracle MySQL Cloud Service and click the "Create Service" button.
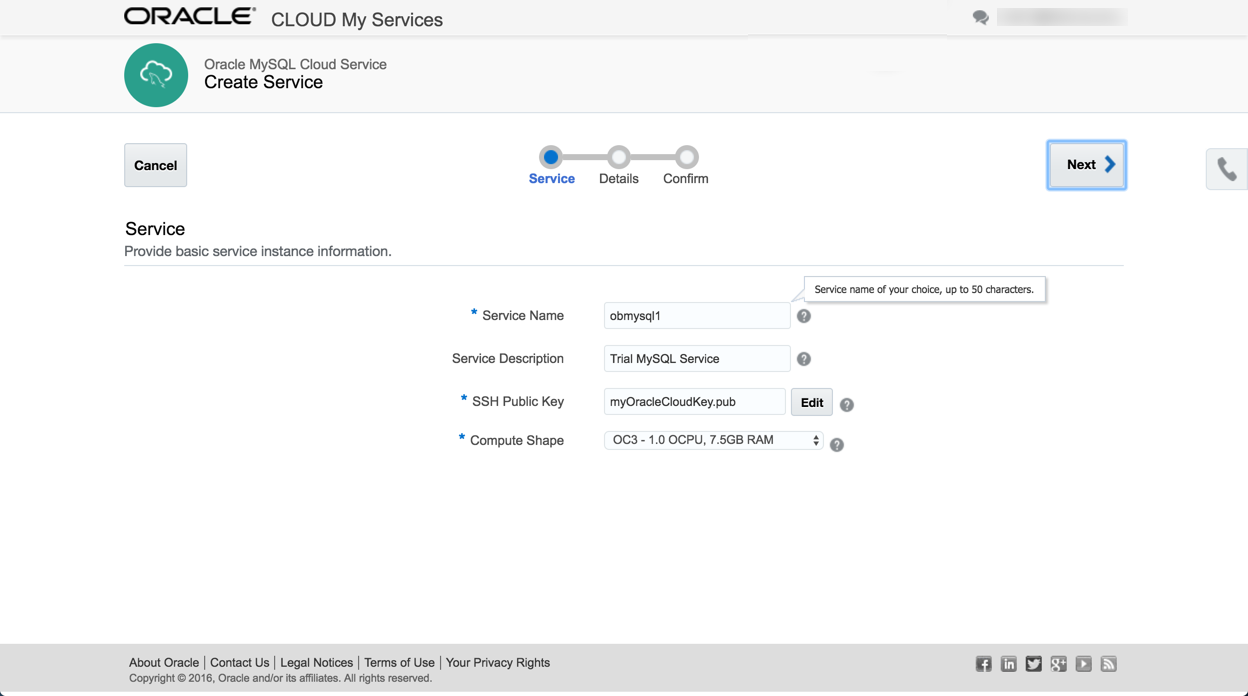
Enter the service name, upload the SSH public key by clicking the "Edit" button, select the compute shape and press the "Next" button.
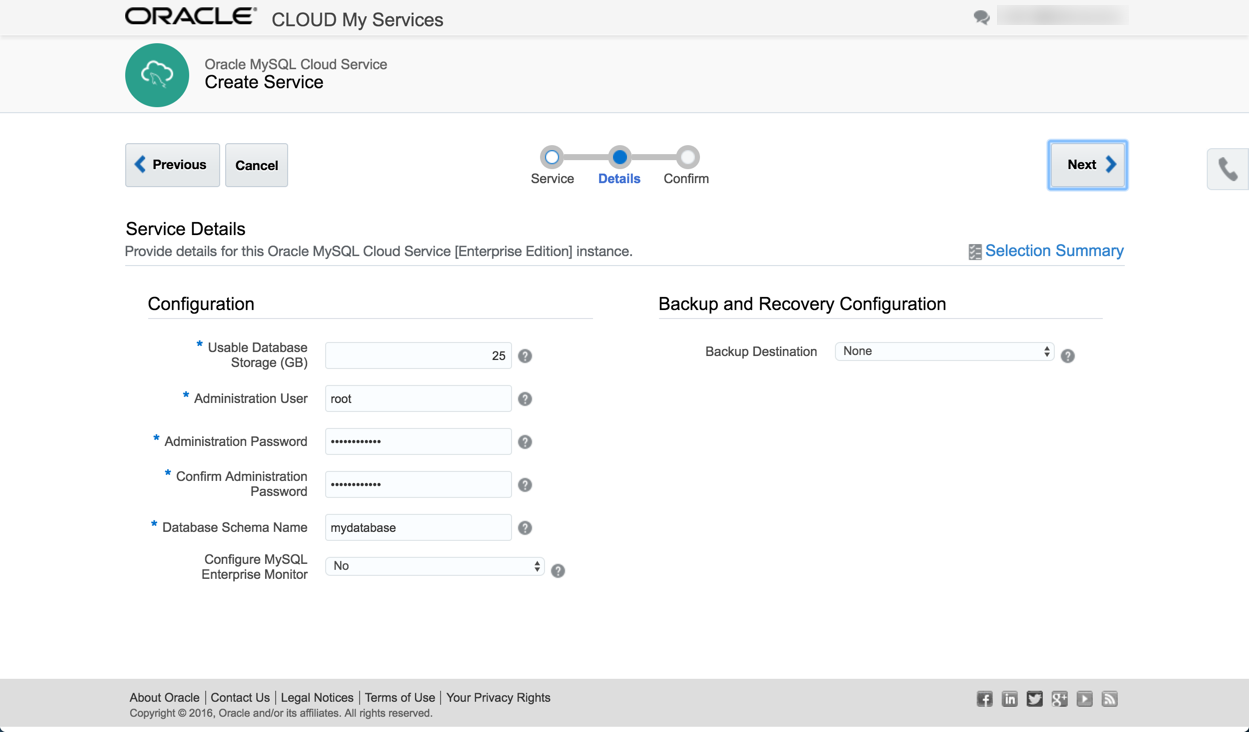
Enter the service details and click the "Next" button. For a quick test, select "None" for the backup destination.
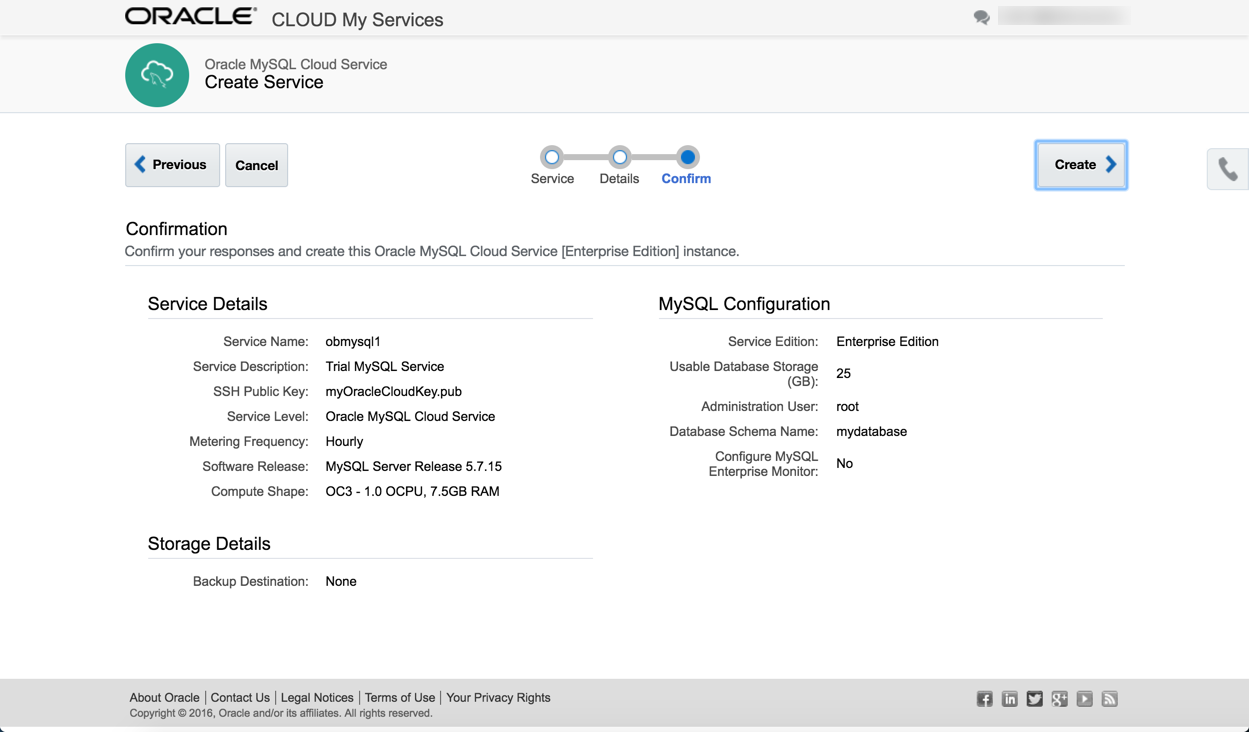
If you are happy with the details on the confirmation page, click the "Create" button.
Wait while the service is created.
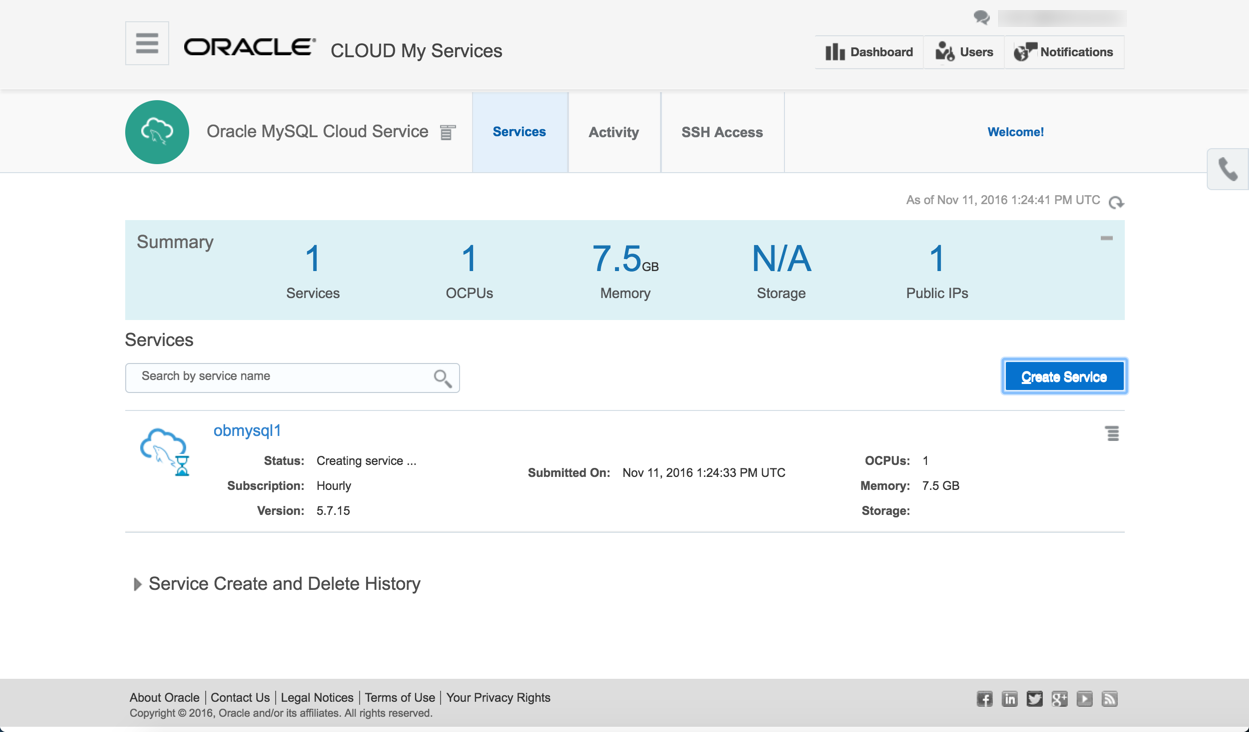
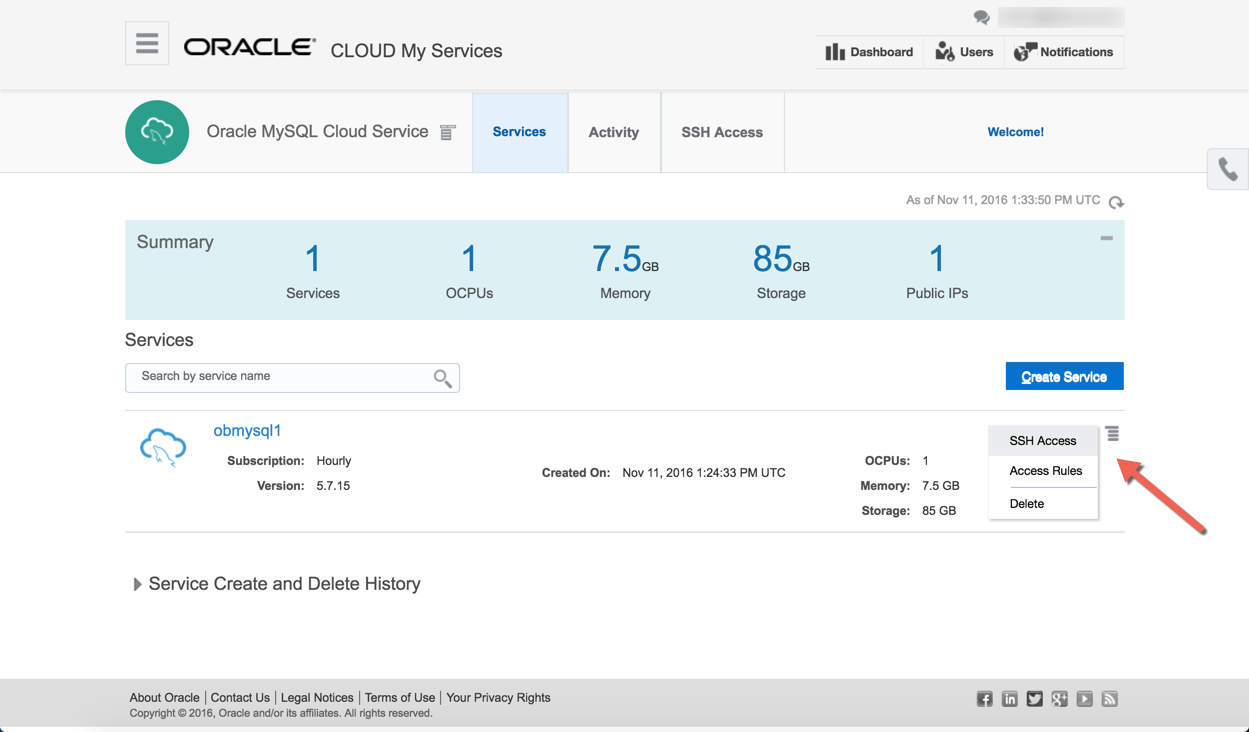
Once the service is created the hamburger on the right of the service allows you to configure SSH access, define access (firewall) rules or delete the service. Clicking on the service name allows you to drilldown to the service details.
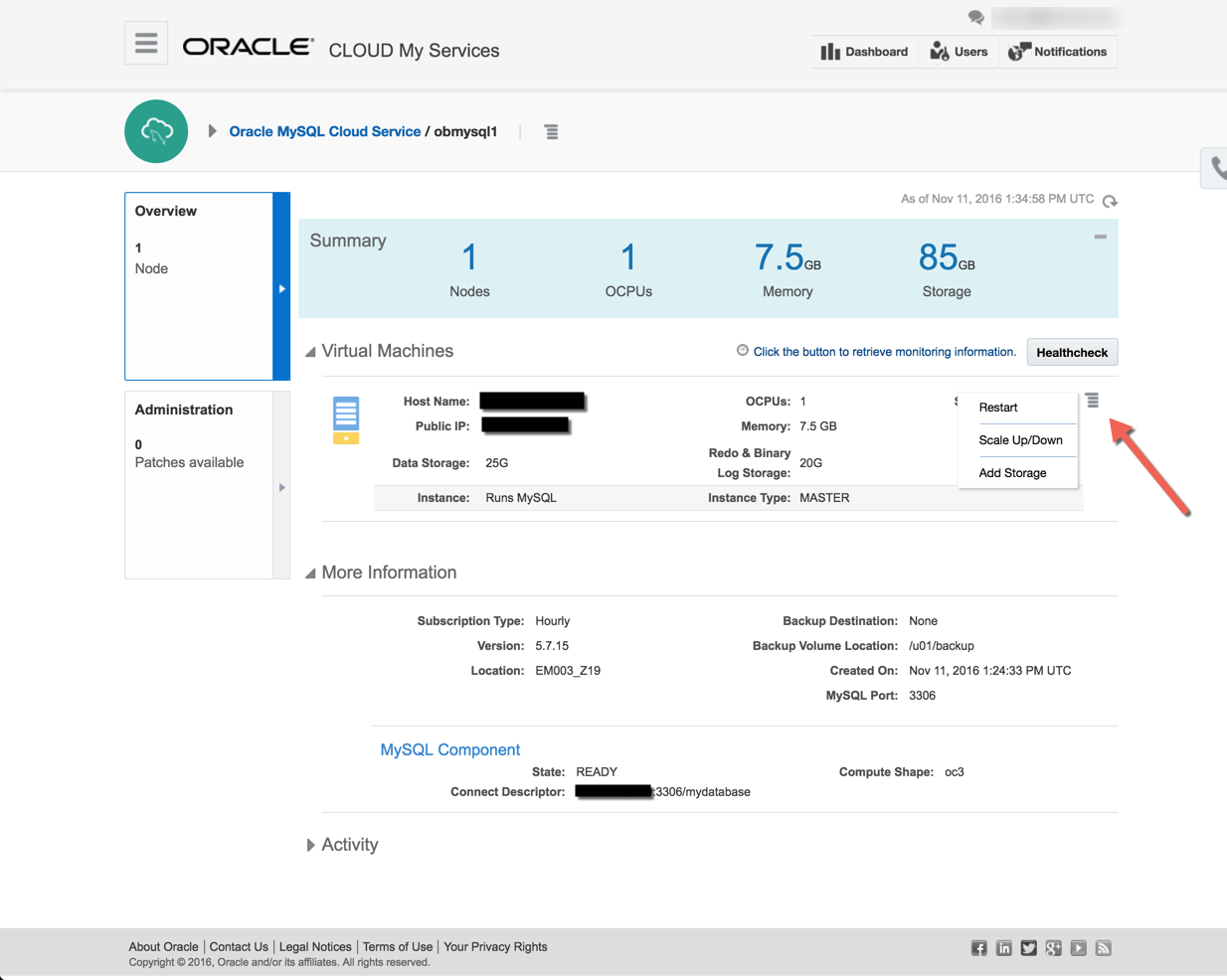
The summary screen allows you to see more details of the service. The administration panel allows you to see available patches if present. The hamburger on the right side allows you to restart the service, scale up/down the service and add storage. Further down the page are the connection details.
Connecting to the VM using SSH
Most of the time you will probably be connecting to the "opc" operating system user. You do this by specifying your private key and connect to the "opc" user on the public IP address from your service detail page.
$ ssh -i ./myOracleCloudKey opc@123.123.123.123 ******************************************************************************** * Welcome to * * MySQL Cloud Service * * by * * Oracle * * If you are an unauthorised user please disconnect IMMEDIATELY * ******************************************************************************** ******************************* MySQL Information ****************************** * Status: RUNNING * * Version: 5.7.15 * ******************************************************************************** ************************** Storage Volume Information ************************** * Volume Used Use% Available Size Mounted on * * MySQLlog 6.1G -------- 33% 13G 20G /u01/translog * * bin 2.6G ------- 28% 6.7G 9.8G /u01/bin * * data 122M -- 1% 24G 25G /u01/data * ******************************************************************************** [opc@################ ~]$
Use the sudo command to perform tasks as the root user. You can access MySQL by switching to the oracle user.
[opc@################ ~]$ sudo su - oracle [oracle@################ ~]$ mysql Welcome to the MySQL monitor. Commands end with ; or \g. Your MySQL connection id is 44 Server version: 5.7.15-enterprise-commercial-advanced-log MySQL Enterprise Server - Advanced Edition (Commercial) Copyright (c) 2000, 2016, Oracle and/or its affiliates. All rights reserved. Oracle is a registered trademark of Oracle Corporation and/or its affiliates. Other names may be trademarks of their respective owners. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. mysql> show databases; +--------------------+ | Database | +--------------------+ | information_schema | | mydatabase | | mysql | | performance_schema | | sys | +--------------------+ 5 rows in set (0.00 sec) mysql>
Firewall Rules
The MySQL services are run under the Oracle Compute Cloud (IaaS). This has it's own firewall configuration, allowing you to limit access to your services. By default, all endpoints except SSH are disabled. There are a number of predefined "Security Rules" to open up the assorted endpoints, but they typically open the endpoints to public, which is rather risky. Instead, you should define custom rules, opening access to ports from specific machines.
- Navigate to the main "Oracle MySQL Cloud Service".
- Click on the hamburger next to the service of interest.
- Click the "Access Rules" option on the popup menu.
- Click the "Create Rule" button.
- Enter a "Rule Name".
- Select "
" as the "Source" and enter your IP address in resulting box. - Select "mysql_MASTER" as the "Destination".
- Enter "3306" as the "Destination Port(s)".
- Leave "TCP" as the "Protocol".
- Click the "Create" button.
Connecting to MySQL From a Remote Client
You should now be able to connect to the service using a MySQL client on your PC.
C:\>mysql --host=123.123.123.123 --user=root --password Enter password: ************ Welcome to the MySQL monitor. Commands end with ; or \g. Your MySQL connection id is 35 Server version: 5.7.15-enterprise-commercial-advanced-log MySQL Enterprise Server - Advanced Edition (Commercial) Copyright (c) 2000, 2015, Oracle and/or its affiliates. All rights reserved. Oracle is a registered trademark of Oracle Corporation and/or its affiliates. Other names may be trademarks of their respective owners. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. mysql>mysql> show databases; +--------------------+ | Database | +--------------------+ | information_schema | | mydatabase | | mysql | | performance_schema | | sys | +--------------------+ 5 rows in set (0.01 sec) mysql>
For more information see:
Hope this helps. Regards Tim...